Security is a primary concern of businesses, consumers and enterprises throughout the world. With news reports of hacks, data breaches and stolen identities, trust is at an all-time low. And that’s a good thing, especially when it comes to cybersecurity.
Today’s cybersecurity-sensitive companies are actively introducing new security layers to their users’ workflows to thwart hackers. One of the primary lines of defense is multi-factor authentication (MFA), or one of its specific variations, two-factor authentication (2FA).
We strongly recommend that every organization implement either multi-factor authentication or two-factor authentication, especially if your organization handles sensitive data. We’ll explain why in a minute, but first, let’s take a step back and define multi-factor authentication and two-factor authentication.
=====
Editor’s Note: Are you looking to improve the security posture of your organization? Download our FREE Cybersecurity Toolkit, which includes handy desk reference guides, posters and checklists that you can share with your teams.
=====
What is two-factor or multi-factor authentication?
Multi-factor authentication, MFA for short, is an added layer of security that requires the extra step(s) of verification in addition to a user submitting their credentials (username and password). These additional verification steps are something only the user would know, have on them or have access to. Multi-factor authentication simply indicates that there are multiple verification methods in place. It could be two steps, three steps, five steps or more.
Two-factor authentication (2FA) is a subset of MFA in that only two verification steps are required to confirm a user’s identity. When configured correctly, two-factor authentication is sufficient in verifying a user’s identity and defeating credential hacks. When you require three or more steps, you’ll slow down users’ login times, which could lead to user frustration with diminishing security gains.
If your organization has subscribed to Netgain’s Security-as-a-Service offering (SECaaS), 2FA comes standard.
How does multi-factor authentication and two-factor authentication work?
There are three buckets of authentication categories, and you’ll need to select authentication methods from at least two of the three categories to be 2FA- or MFA-compliant.
What You Know
This category includes knowledge that is retained and only known by you. The most common example of this is a password, a PIN or a passphrase. Some organizations consider security questions (e.g. “What is your mother’s maiden name?”) part of this category, but since answers to these questions can sometimes be public knowledge or attained via social engineering, they’re not a reliable authentication method.
What You Have
While passwords can be hacked via digital methods, physical items that you hold in your possession are much harder to hack. So, by verifying a user’s identity based on physical items, a login attempt can be verified. This includes mobile phones, physical tokens, key fobs, smart cards, network access and more.
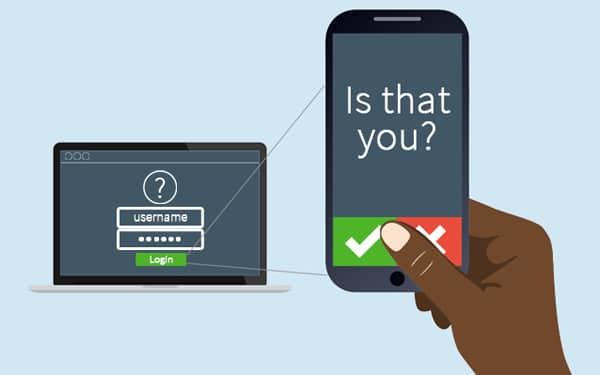
One of the most common two-factor authentication workflows includes a password from the What You Know category and a text message from the What You Have category. You may have experienced this before when you’ve tried to log in to services you use at home. You provide your username and password on a login screen, then receive a text message of a push notification (via a service like Duo) to your mobile device with a code to enter on the login screen. It’s a quick verification process that confirms it is, in fact, you who is logging in.
What You Are
This category is less common in everyday situations but is often leveraged in highly secure environments. This category includes unique identifiers that very specific to your physical person. The most common identifier is a fingerprint, but it could also be a retinal scan, voice or facial recognition or any other biometric identifier.
Why do I need two-factor or multi-factor authentication in my firm or practice?
Organizations that are trusted with incredibly sensitive data—protected health information, financial information and personal identity information—are at an increased risk of attack from hackers. Rather than hacking specific individuals to get a single data record, hackers focus their attention on hacking an organization that has access to hundreds, thousands or millions of data records.
The rise of bring-your-own-device (BYOD), increased mobility and cloud-based applications have changed the security game. Usernames and passwords used to be an adequate security measure to ward off cyber-hackers, but not anymore. Additional forms of authentication are needed so only authorized users can access secured data on authorized devices.
When your users demand anytime/anywhere access to their applications, information security becomes the greatest concern for organizations. In these instances, organizations are forced to balance instituting top-tier security protocols against offering their users the tools to work efficiently and effectively.
Relying solely on the user’s ability to safeguard that data is irresponsible. Hackers have gotten incredibly effective at exploiting human vulnerabilities to access systems, so adding additional technical protections like 2FA and MFA add another layer of security while allowing users the flexibility to work anytime and anywhere.
How do I implement 2FA for my users?
Good news! Depending on the Netgain Security Services to which you already subscribe, you may already have access to two-factor authentication, though it may not be implemented yet. Simply reach out to your Netgain Account Manager to discuss access to this security tool and others you may want to consider implementing.
As security remains a critical factor for the healthcare organizations, financial services firms and law firms that Netgain serves, our Security and Innovation Teams will continue to find solutions that enhance the security of your data.