Search results for: “vulnerability”
-

Takeaways from the Boomer Consulting BTC Summit 2022
Wow, what a week. The Netgain Fintech team attended a well-organized and executed Boomer Consulting’s BTC Summit 2022 event at a fantastic new location, the Loew’s Hotel in Kansas City’s…
-

Inside Netgain: Meet Diane Ellis, Senior Billing Data Analyst
Q: What is your role at Netgain? Diane: My role is to manage the order to cash process. This involves managing all things that go into the maintaining the various…
-
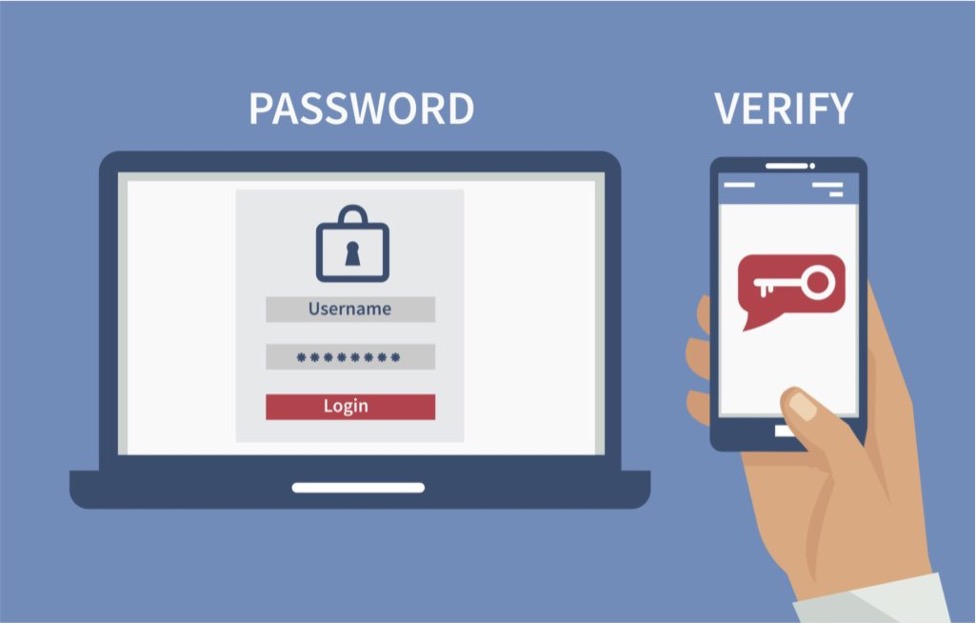
Three Tips on Why Multi-Factor Authentication is Critical to Data Security
Cybercrime is rife in 2022. Kaspersky released a new report revealing a growing number of cyberattacks on small businesses so far in 2022. Researchers compared the period between January and April 2022…
-

Security Lesson #6: What Are Endpoints and How Do You Secure Them?
In our last post, we talked about application security and how the security measures at the application level prevent data or code within the application from being stolen or hijacked.…
-

Netgain Employee Spotlight: Kshitij Kathuria, CISO
Recently, we sat down with our newest executive team member Kshitij Kathuria, who joined recently as Netgain’s new Chief Information Security Officer. In this interview, we discussed the meaning of…
-

The Key to an Effective Client-MSP Partnership
In my discussions with our clients, I often hear that we are a “seamless extension of their IT”, not a replacement. This is especially gratifying given the increasingly complex and…
-

Security Lesson #2: Risk Assessment Checklist
This post on questions that drive your cybersecurity strategy is the third post in our new Security Lessons series. To start from the beginning, read “What we learned as a…
-
Security Lesson #1: 9 Foundational Questions That Drive Your Cybersecurity Strategy
This post on questions that drive your cybersecurity strategy is the second post in our new Security Lessons series. To start from the beginning, read “What we learned as a…