Joining the Ranks of Cyberattack Victims
Microsoft. Marriott. Equifax. FireEye. The US Government. Netgain.
All of these organizations have one unfortunate common thread: They – we – have all been victims of cyberattacks. In our case, late last year, Netgain was the victim of a criminal ransomware attack.
To be clear, the threat to our environment was contained and eradicated in December, and Netgain restored services for its impacted clients. In addition, our cybersecurity experts have been monitoring for any signs that the data has been misused. To date, no such indications have been identified.
Unfortunately, as the long list of well-publicized victims of such attacks makes clear: No company or government agency is immune to cyberattacks, and such attacks remain a growing threat to every organization.
A Stronger Security Posture
Yet, to become a victim of such an attack is both humbling and galvanizing. Our comprehensive, multi-platform backup strategy was battle tested and proved effective. In addition, we identified additional opportunities to strengthen our security posture in a continuous journey with an ongoing commitment to ensure this remains top-of-mind.
As part of our incident response, we have implemented a number of these identified enhancements to our security posture and have continued to progress a multi-pronged approach. We’ve deployed new tools, revised policies and enforcement procedures, and implemented an advanced around-the-clock managed detection and response service for proactive threat monitoring.
A Deeper Look into Security
Having navigated an attack like this with both internal and external expertise by our side, we have not only emerged stronger but have harvested significant insights. We would like to do our small part in advancing broader cybersecurity awareness and education given the exponentially escalating nature of these cyber-threats.
Over the coming weeks, we’ll be publishing a series of blog posts to help inform, educate, caution, and advise our readers of key considerations and best practices to keep in mind.
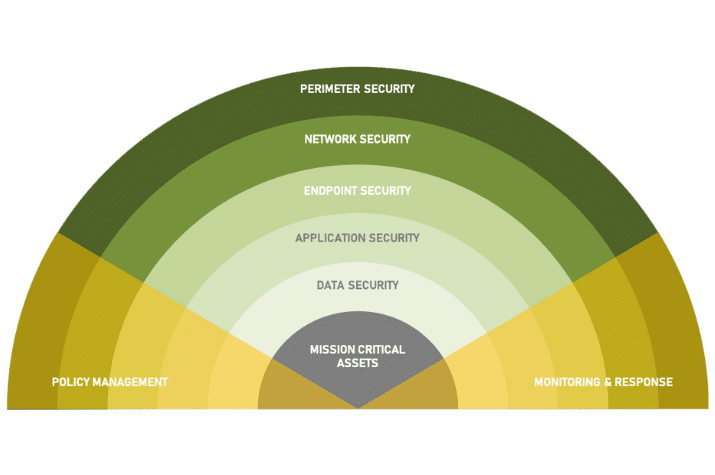
We’ll structure the discussion using a layered security model we have adopted for our own security roadmap. This includes:
- Perimeter Security
- Network Security
- Endpoint Security
- Application Security
- Data Security
- Policy Management & Enforcement
- Monitoring & Response
Within each security layer, we’ll explain that layer’s purpose, and highlight:
- Common security mistakes organizations can make
- Minimum security measures every organizations should take
- Best practices around security that organizations should consider

Some of our recommendations will be familiar – who hasn’t heard of multi-factor authentication? – but will be no less important for being familiar. (According to at least one survey, 78% of Microsoft 365 administrators do not have multi-factor authentication activated)
We’ll also talk about security philosophies and mindsets – least-privilege and zero-trust for example – and the steps you can take to help improve security in your organization – regardless who manages your IT infrastructure.
Shared Responsibility for Security
For too long, managed service providers and technology partners (including us) have taken the stance of shielding our clients from the headaches, intricacies, and complications that a strong security stance involves. While it’s true that we can significantly reduce the burden of security on our clients and their teams, the responsibility is still shared. We owe it to our clients to ensure they not only understand the steps we’re taking as their IT partner, but also the measures that require their active participation and consent.
We hope this series of blog posts will help form the basis for those conversations, and we’re looking forward to more discussions to come.