Blog Library
IT Insights Grounded in Real-World Experience and Industry Context
-

SOC 2 Type II vs. ISO 27001 for MSPs: What Actually Matters Across the CIA Triad
If your CPA firm is evaluating a managed service provider for IT-as-a-Service, security is usually the headline. But it is not the full story. For firms handling client financial data,…
-
The Hard Part of AI for CPA Firms Isn’t the Technology
AI is becoming part of everyday decision-making inside CPA firms, not because firms are chasing trends, but because the pressure is getting harder to ignore. Clients are asking different questions.…
-

After Busy Season: What Broke in Your CPA Firm and What to Fix Before Next Year
Busy season didn’t create new problems for CPA firms. It exposed the ones that were already there. Long hours, tight deadlines and constant client demands are expected. In many firms,…
-
Why Data, Not Budget, Is Slowing AI Adoption in CPA Firms
Most CPA firms are not struggling to access AI. They are struggling to use it in a way that actually changes how work gets done. Over the past year, firms…
-
What Cyber Insurance Underwriters Are Actually Requiring from CPA Firms in 2026
Cyber insurance used to feel like paperwork. In 2026, it feels more like an audit. Renewal applications are longer. Questions are more technical. Underwriters increasingly want evidence, not just yes…
-
How CPA Firms Can Lower IT Risk Without Increasing the Budget
Most breaches in mid-sized firms do not happen because the firm lacked a tool. They happen because no one owns enforcement. That distinction should change where leadership focuses. Many CPA…
-
Netgain Accepted into BDO Alliance USA Vendor Marketing Program to Expand Access to Secure Technology and AI for CPA Firms
Alliance member firms can access Azure-based managed IT, 24/7 cybersecurity operations and AI expertise Minnetonka, MN – Feb. 24, 2026 – CPA firms face increasing pressure to strengthen their technology environments, defend against…
-
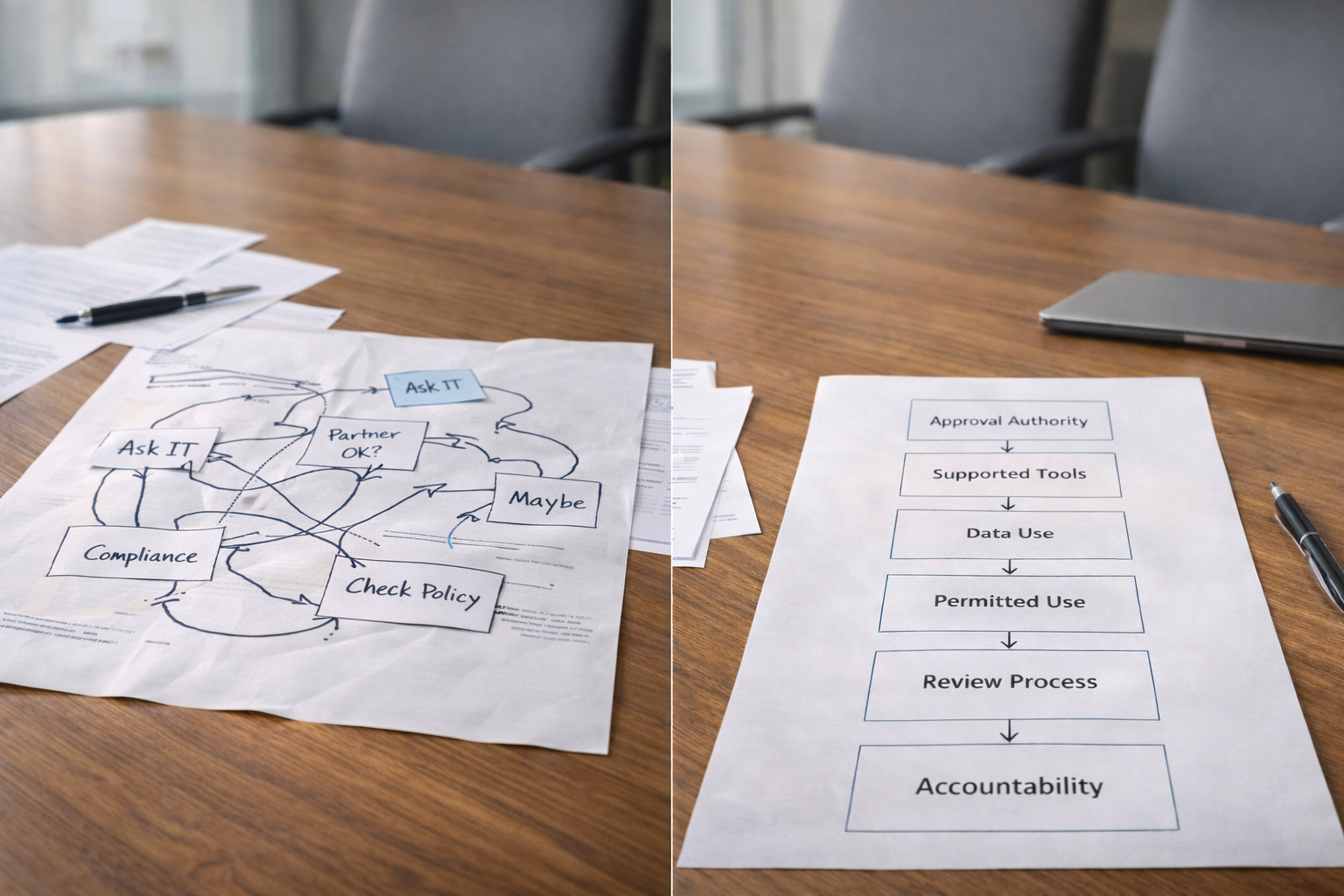
You Already Have AI Governance. It’s Just Not Working the Way You Think.
With or without a formal AI policy, every CPA firm is already making AI decisions. This article is about recognizing that reality and understanding why unclear governance quietly stalls AI…
-
Netgain Named to CRN’s 2026 MSP 500 List for Sixth Consecutive Year
Recognized in the Pioneer 250 Category for Excellence in Managed Cloud, IT and Cybersecurity Services Minnetonka, MN – Feb. 12, 2026 – Netgain Technology, LLC, a premier provider of managed cloud, IT and cybersecurity solutions for accounting firms, healthcare organizations and legal practices, announced…
-
AI Access Is Not AI Adoption: Why CPA Firms Stall After Buying the Tools
For many CPA firms, the AI journey starts with good intentions and a credit card. A Copilot license here, a ChatGPT account there, maybe even a firmwide announcement that “we’re…
-
A Practical AI Timeline for CPA Firms During Busy Season
When CPA firms struggle with AI during busy season, it’s rarely because the technology failed. More often, decisions were made too late, under too much pressure, or without clear ownership.…
-
AI Mistakes and Guardrails Every CPA Firm Needs During Busy Season
Once AI is in use, even in limited ways, the conversation shifts quickly. It is no longer about whether AI can help. It is about how easily it can create…
Let’s Talk About Your IT Needs
Ready to take IT off your plate and focus on growing your business?