Search results for: “data”
-

Inside Netgain: Meet Demetri Booras, Senior Field Services Technician
Q: What is your role at Netgain? Demetri: I wear many hats and have had varying responsibilities across many different projects. However, my current title is a Senior Field Services…
-

How Modern Accounting Firms Are Solving the Capacity Conundrum Webinar
Join Pat Morrell, Chief Revenue Officer with Aiwyn, Bob Lewis, President of The Visionary Group and Kate Krupey, VP of Accounting with Netgain for this webinar as they discuss how…
-

The Automation Advantage
Automation is no longer a buzzword, and spurred by the global pandemic, firms of all sizes are discovering the importance of moving away from manual, labor-intensive tasks. Resiliency, speed, productivity,…
-

Netgain Recognized on CRN’s 2023 MSP 500 and Managed Security 100 Lists
Accounting, Healthcare, and Legal cloud provider named to the Security 100 for third year in a row Minnetonka, MN, February 15, 2023 — Netgain Technology LLC, a cloud solutions provider…
-

Inside Netgain: Meet Jim Riedeman, Client Services Solution Architect
Q: What is your role at Netgain? Jim: I am a Client Services Solution Architect at Netgain. Q. What does your day-to-day typically look like? Jim: My days are very…
-
The 80/20 Rule: Balancing Innovation with Operational Execution
Traditional client satisfaction metrics (CSAT, NPS) provide useful insights into value created by managed services providers (MSP), but they are not the most important metric. Instead, the question that we…
-

Netgain Technology Named on ChannelE2E Top 100 Vertical Market MSPs: 2022 Edition
Seventh-Annual List Reveals Leading MSPs In Healthcare, Legal, Government, Financial Services & More April 25, 2022 – Minnetonka, MN: Netgain Technology LLC, an industry-aligned cloud solutions provider focused on serving…
-

Netgain Technology Recognized on CRN’s 2022 MSP 500 List
Accounting and Healthcare cloud provider named to the Security 100 for second year in a row St. Cloud, MN, February 16, 2022 — Netgain Technology LLC, a cloud solutions provider…
-
Microsoft Inspire: Key Takeaways from Day 1
While we miss the buzz and adhoc interactions with likeminded partners working in equal earnest to position themselves for the ever-expanding digital transformation opportunity, this year’s Inspire started off on…
-

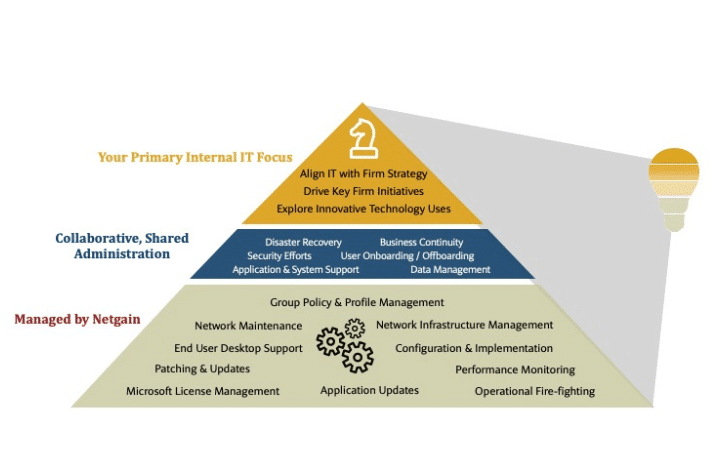
Making IT Strategic to CPA Firm Direction
Whether your CPA firm’s strategic direction anchors around traditional merger & acquisition strategies, organic growth through a defined marketing plan, the delivery of new services and offerings, or some other…
-

The New Internal IT: Driving Strategic Initiatives & Finding Capacity in 2021
This year, Netgain was a proud gold sponsor at Wolters Kluwer’s CCH Forward Together Virtual Conference. At the conference, our team interacted with attendees through our virtual booth and presented…
