-
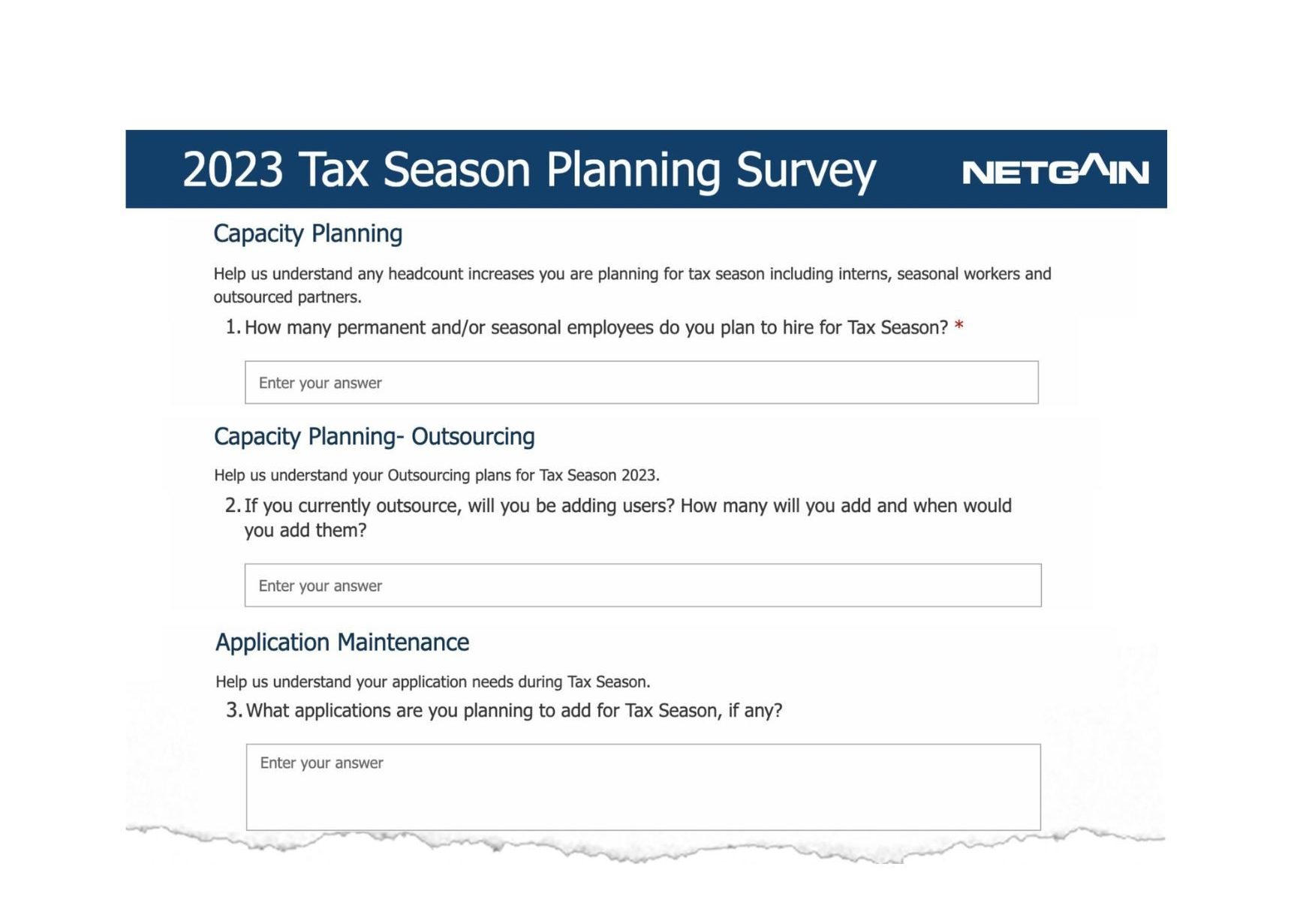
Five IT Planning Considerations as CPA Firms Head into Tax Season
Preparing for tax season seems to be a season itself. As accountants are busy with tax planning, other business units have their own checklists and planning to do, not the…
-
The Role Technology Plays in your 2023 M&A Strategy
During this webinar, we explored what a successful M&A looks like from both the business and technology perspectives with industry thought leaders Bob Fink, IT Partner & CIO at Honkamp,…
-
Application & Desktop Virtualization Options for CPA Firms
When looking at the options for your CPA firm around virtualization and cloud implementation, you may be wondering how desktop hosting and virtualization options stack up against each other. Netgain has analyzed…
-
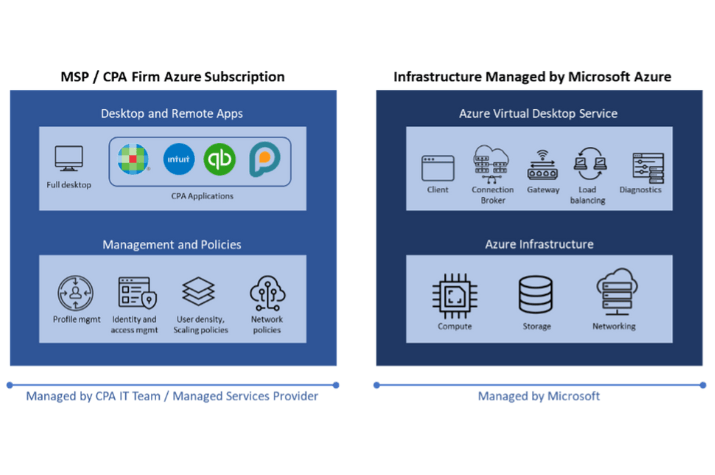
How Azure Virtual Desktop is Redefining Collaboration in the CPA Vertical
As a Cloud Managed Services Provider (MSP) focused on the CPA profession, we work extensively with CPA firms to manage their IT infrastructure and deliver a virtual desktop solution that…
-
Takeaways from the Boomer Consulting BTC Summit 2022
Wow, what a week. The Netgain Fintech team attended a well-organized and executed Boomer Consulting’s BTC Summit 2022 event at a fantastic new location, the Loew’s Hotel in Kansas City’s…
-
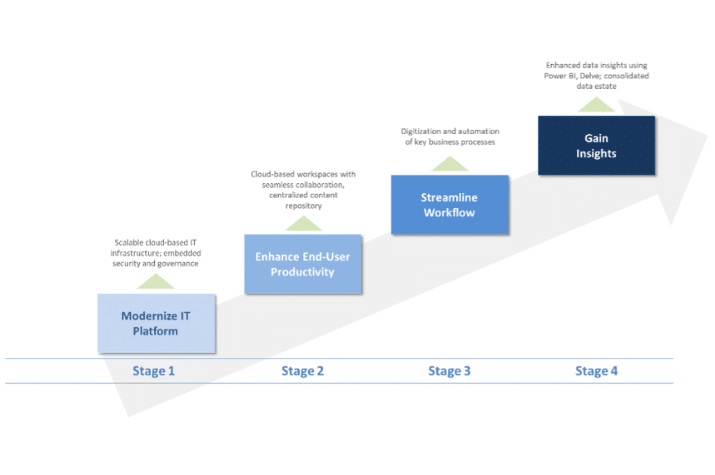
CPA Firm of the Future – Is your Infrastructure Ready? 3 Things to Consider
1. Tech intensity is key for firms to adapt and thrive CPA firms today are navigating several common challenges as they seek to expand their advisory services through organic growth,…
-
AICPA Engage 2022 Conference – An Overview from a Technology Provider’s Perspective
It was great to be back in person at AICPA’s Engage Conference last week in Las Vegas! As a provider to the CPA profession, I was excited to see the…
-
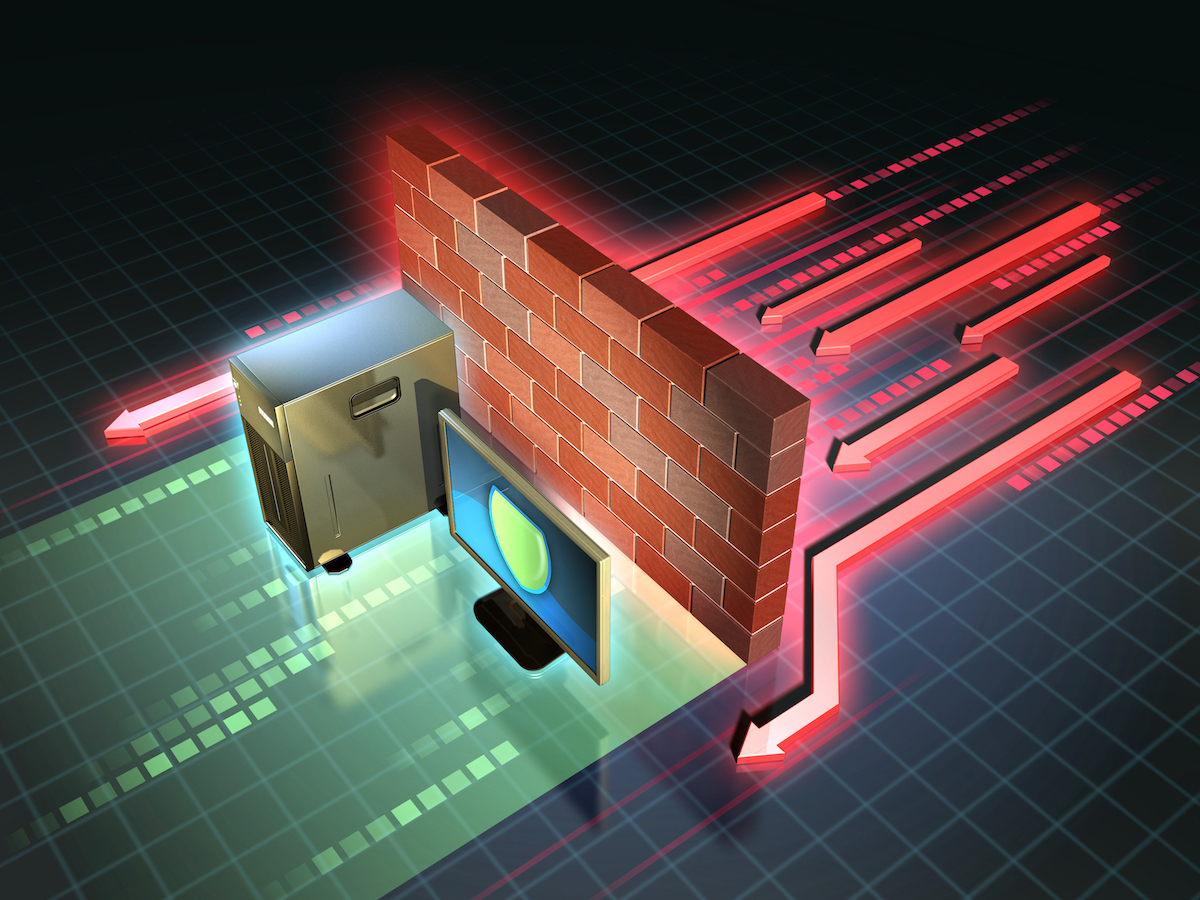
Security Lesson #7: The Essentials of Implementing Effective Perimeter Security
As I highlighted in my first post, no company or government agency is immune to cyberattacks, and these attacks are a growing threat to every organization. To protect against these attacks, you need…
-
Security Lesson #6: What Are Endpoints and How Do You Secure Them?
In our last post, we talked about application security and how the security measures at the application level prevent data or code within the application from being stolen or hijacked.…
-
Security Lesson #5: How to Think about Your Application Security Strategy
This is the latest post in our Security Lessons series. In my last two posts, I explained what data security is and outlined data security best practices. In this post,…
-
Tax Season 2022 Planning – Spotlight on Communications
With tax season 2022 fast approaching, how are you doing with final stretch preparations? While many core processes will be repeated with the deftness and confidence that only years of…
-
Security Lesson #4: Build Your Data Security Strategy on Best Practices
The data security layer is about protecting the data you have. It includes the different cybersecurity practices that you use to secure your data and prevent data breaches and misuse.…